转载声明
本文为灯塔大数据原创内容,欢迎个人转载至朋友圈,其他机构转载请在文章开头标注:“转自:灯塔大数据;微信:DTbigdata”
Darktrace公司的首席技术官戴夫·帕尔默是防御网络威胁方面享誉国际的领导人物,他认为科技的进步已经使我们的社会进入一个“犯罪的黄金时代”。这种说法不无道理,因为几乎每天我们都能看到勒索软件、信用卡信息泄露、身份盗窃、分布式拒绝服务攻击占据头版头条。众所周知,遭遇网络犯罪攻击的品牌会蒙受重大损失,很多品牌在遭到攻击后并没有选择曝光,而是和攻击方签订协议,防止负面消息爆出。尽管媒体大部分的关注点还在针对金融服务领域的攻击方面,但能源、国防、科技、电信甚至是教育行业都面临着攻/击的威胁。
诈骗犯——科技发展居然为虎作伥毕马威会计事务所的一项调查显示,全世界750起诈骗案中,只有190起主要原因是内部控制薄弱。然而,即使是内部控制完好且高效的公司,诈骗犯依然能够对他们下手。通常来说,复杂的监测系统需要高层管理人员授权验证,但诈骗活动多为告密者或可疑的商家所致。诈骗犯大多数情况下团伙作案,因为需要多人合作才能绕过控制系统,黑入某个系统。上述的调查报告显示,典型的网络诈骗犯通常为男性(数据显示,每6个诈骗犯中5个都是男性),年龄36岁到55岁之间,且在被攻击公司中担任管理职位,如管理部门、金融部门或者综合管理部门。
毕马威会计事务所这份调查报告中显示,科技日益成为诈骗的重要驱动,24%的诈骗犯利用科技进行犯罪。IBM公司的一项研究表明,在调查的多起信息泄露事件中,47%是黑客和内鬼所为。网络攻击的频率增多,被认为是信息外泄损失增多的最主要原因。尽管很多新闻标题都声称网络诈骗是真实存在的威胁,且已迫在眉睫,但是此项调查发现很多公司都过于自信,根本没有做好应对潜在的网络威胁的准备。
最近的网络诈骗数据IBM公司的调查显示,平均每起信息泄露造成的损失约为380万美元(约2527.6万人民币)。普华永道会计事务所一项犯罪调查报告发现,28%加拿大人承认在最近两年内参与过网络犯罪。朱尼普研究公司估计,2020年网上交易诈骗金额与2015年比将翻倍,从106亿美元(约705亿人民币)暴增至250亿美元(约1662.9亿人民币)。电子零售行业被认为是网络犯罪的下一个大目标,预计到2020年,该领域的网络交易诈骗将卷走超过166亿美元(约1104.1亿人民币)。朱尼普的报告中还估计公司企业在网络诈骗监测手段上的投入将增加30%,增长至92亿美元(约611.9亿人民币)。银行业和医疗行业的诈骗全球最大银行组织之一环球银行金融电信协会近期承认,他们遭受了2016年以来第2次网络攻击,诈骗犯黑进了连接11,000个银行的通信系统,并通过操纵银行和该协会的联系盗取了其中一家银行的钱。另一起袭击发生在孟加拉国的一家商业银行,他们通过内部人员操作盗取证书,偷走银行8100万美元(约人民币5.38亿人民币)。医疗行业也同样面临着危机,大量网络诈骗把目标对准了这一领域。这其实是意料之中的事,网络上有数百万条医疗记录,对于信息窃贼来说这是块大肥肉。2015年,美国第二大保险公司“Anthem”公司报告了一起信息泄露,8千万客户的姓名、收入信息、社会保险号、医疗身份证号等其他隐私信息被盗。另一家国家医疗供应商“卫生系统”公司,也报告了一起精心谋划的攻击,2014年4月至6月间,450万患者和公司雇员的信息被非法入侵、非法拷贝、非法转移。虽然大部分黑客并不会直接使用他们偷到的数据,但是他们会转卖给暗网买家,通常他们会将同一数据库卖给多个买家。这些数据之后就被用来捏造虚假患者诉求,蒙骗保险公司和政府卫生部门,也可能被用于通过偷来的账号购买处方药。下图就是一个暗网买家通过黑客购买医疗保险信息。
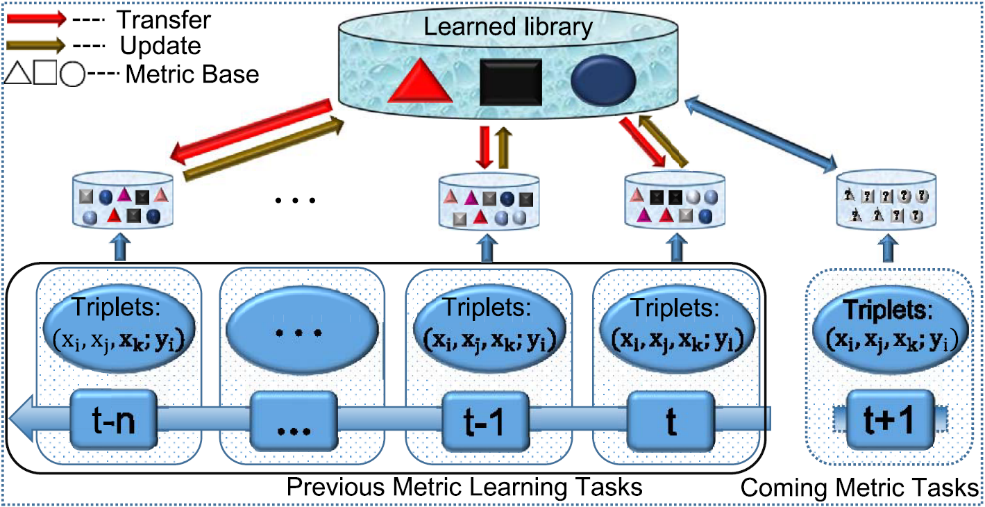
分析技术监测诈骗监测和预防是打击诈骗的两种方式。诈骗监测系统可以识别企图诈骗行为,而诈骗预防系统则是为了防止诈骗发生。如果两种方法同时使用,预防系统就会让黑客改变策略,这就影响了监测系统的能力。同样,监测系统会致使黑客设计更新颖的方式获取隐私信息,这就削弱了其本身的监测能力。诈骗分析领域的专家,诈骗监测专著作者巴特·巴森斯认为,监测、减少诈骗活动的技术包括描述性分析、预测性分析和社交网络分析。描述性分析可以运用关联规则、归并规则和对等体组分析等手段来追踪反常行为。预测性分析可以通过过去发生的真实诈骗汇报数据来创建诈骗监测模型,之后用于监测实时数据诈骗。时间越长,模型就能学习更多新的网络攻击的类型。用于分析诈骗数据的技术包括神经网络,随机森林和线性回归/罗吉斯回归。越来越多的公司选择运用社交网络分析来对抗诈骗。社交网络分析可以综合不同功能来监测诈骗类型,更早发现由个别部门导致的漏洞。这是一种先进的可视化能力和分析能力,能够让公司来发现与预防网络诈骗和传统商业渠道的诈骗。诉讼数据分析工具当下,大部分公司都要处理大量网络敏感数据,他们都清楚网络诈骗的威胁,一套更为复杂的反诈骗技术将会被使用。但是,EY的一项研究显示,很多公司依然在使用传统的描述性技术来进行诉讼数据分析,在使用SAS,Hadoop和ACL等更先进技术上明显滞后。很多公司认为,无法更新技术的原因之一是没有技术过硬的员工来操作更为复杂的技术。
网骗战场,哪些公司在战斗?通常会计师深入分析数据,通过发现重复数字和总数差异,发掘背后的原因来识别诈骗类型,而这些都需要数据分析的支持。会计公司通常用本福特定律来检测异常,该定律称:至金融交易数据中有30.1%会以数字1开头。其次是以数字2开头的,以此类推。这一技术在安然公司2000年财务报表中得以运用,本福特定律的变形规律在其中也有运用。
从2011年起洛杉矶就一直在使用统计分析系统来识别虚假社会服务诉求。他们运用预测性分析、社交网络分析和一般分析学来分析社交网络,计算儿童福利项目出现欺诈的可能性。社交网络分析在其中扮演了非常重要的角色,因为它能让调查员轻松定位之前没被发现的电话号码和地址的匹配关系。
“纪念卫生系统”是美国第二大的公共医疗网络,每年都会为商家提供大量的人工数据文件。通过与IBM合作,他们研发出了VETTED,一套商家资格认证系统,这能帮助他们的员工更好的发现合作商的活动,在决策之前能够更深入的剖析洞察。这套系统成功地发现了3个合作商曾针对一项提案密谋锁价保值。同时它还能标出高危商家,提醒利益冲突。未来如何发展?根据德勤公司2015年的调查显示,虽然现在有所进步,但是在接受调查的公司中仍有五分之一没有运用数据科学和分析学来打击诈骗,尽管她们都知道诈骗会越来越多,之后也会越来越难被发现。普华永道的调查显示绝大部分公司并没有准备好应对网络犯罪的袭击。只有37%的公司拥有有效的应对机制,它们当中大部分都属于严格监管的金融部门。近30%的公司并没有具体的应对攻击的方案,它们当中有一半都认为自己足够安全,无需部署防范机制。这项调查认为,大部分公司对这一问题关注不高,原因在于董事会成员对科技方面了解不多,不能正视网络犯罪的威胁。建议企业必须开始重视数据分析在发现、打击网络犯罪上的巨大作用,尤其是在科技为复杂匿名诈骗方案提供温床的今天。如何才能让那些自鸣得意的公司意识到网络诈骗的严重性呢?恐怕只有让他们在周一早晨亲自发现勒索信息,并告诉他们想要回他们的数据,必须购买比特币并存放到安全的地址吧。
结语调查结果显示,不仅所有行业都面临着网络犯罪的威胁,科技手段诈骗造成的损失预计也将在2019年达到2.1万亿美元(约13.9万亿人民币)。网络犯罪不断的占据头条,你可能会觉得这些公司应该会采取措施来保护他们的资产吧?但事实并非如此。他们并没有启用复杂高端的技术工具来打击诈骗,相反,很多公司依然依赖原始的数据分析工具。普华永道调查发现只有37%的公司拥有有效应对机制。除非这些公司一改现在的自大自满,有点忧患意识,否则网络诈骗案件的数量还会不断增长。
英文原文
Industry Insight – Fighting Cyber Fraud with Analytics
IntroductionDave Palmer, CTO of Darktrace, a global leader in cyber threat defence believes that technological progress has propelled society in to a “golden age of criminality”. This is not hard to believe considering news headlines about ransomware, stolen credit cards, identity thefts and DDos attacks have become a daily occurrence. Given that public knowledge of being compromised by a cybercrime can be severely damaging to an organization’s brand, many breaches are swept under the rug or an agreement is reached with the perpetrators to avoid negative publicity. Although the majority of the media attention is devoted to attacks on the financial services sector, the truth is that energy, defense, technology, telecom and even the education sector are vulnerable.图:Statista-Avg annual cost of Cyber Crime(1)Fraudsters – Enabled by TechnologyAccording to a survey undertaken by KPMG, among 750 fraud cases worldwide, 190 cases had weak internal controls as the major contributing factor. However, there were cases where even when the controls were adequate and effective, fraudsters managed to trespass or override them. The fraudulent activity is normally detected by whistleblowers or suspicious vendors, however, a complex detection system is put in place to validate C-suite executives.Fraudsters mostly work in groups because overriding systems usually entails collusion to circumvent controls. This is compounded by the same survey, which revealed that a typical cyber fraudster is usually male (statistically speaking, 5 out of 6 fraudsters are male) in between the ages of 36 and 55, and is an executive member of the victim organization in disciplines such as operations, finance or general management.图:Age of Fraudsters(2)Not surprisingly, the report by KPMG identified technology as an increasing driving force behind fraud so much so that technology was the conduit for 24% of the fraudsters. An IBM sponsored study(3) found that hackers and insiders were behind 47% of the data breaches experienced by participants of the study. The increase in the frequency of cyber-attacks was identified as one of the major contributors to a higher cost of a data breach. Despite the daily barrage of media headlines purporting cyber fraud as a real and imminent threat, the survey found that many companies were complacent and thus unprepared to respond to potential cyber threats.Recent Stats on Cyber Fraud
Cybercrime will become a $2.1 trillion problem by 2019.
Average cost of a data breach was valued at $3.8 million in a study by IBM.A crime survey report(4) by PWC found that 28% of Canadian firms experienced a cybercrime within the last 2 years.Juniper Research estimates online transaction fraud will more than double(5) to $25bn by 2020, from $10.6bn in 2015.E-retail is predicted(5) to be the next big target of cyber criminals and is expected to absorb $16.6 billion in online transaction frauds in 2020.Juniper’s report also anticipates that companies will beef up spending on online fraud detection methods(6) by 30%, rising to $9.2bn in the same period.Recent Frauds in the Banking & Healthcare IndustriesOne of the largest banking organizations in the world, SWIFT, or Society for Worldwide Interbank Financial Telecommunication, recently admitted that it had become a victim of cybercrime for the second time in 2016, when fraudsters broke into a messaging system interconnecting 11000 banks and stole cash from one of the banks by maneuvering connections between the bank and SWIFT network. Another such attack was staged on a commercial bank in Bangladesh in which thieves stole $81 million using comparable tactics of credential theft through insider operations.Similarly, the healthcare space is in a worrisome state, having suffered from numerous cyber fraud incidents. This isn’t surprising, given the presence of millions of healthcare records online – lucrative targets for data thieves. In 2015, America’s second largest insurer, Anthem(7), reported a data breach which compromised names, income data, social security numbers, medical ID numbers, and other confidential information belonging to 80 million subscribers. Another national healthcare provider, Community Health Systems, reported a highly sophisticated attack that accessed, copied and transferred identities of up to 4.5 million patients and employees between April and June 2014.As most hackers don’t have direct use for the data they steal, they sell it to buyers on the deep web, usually selling the same database to multiple clients. This data is then used to file false patient claims with insurers and government health agencies, or purchase preion drugs from a stolen account. The image below shows a buyer in a deep web forum looking to purchase healthcare and insurance data from hacker.图: Cybercrime in Healthcare industry(8)Analytics Techniques for Detecting FraudDetection and prevention are two ways to counter fraud. Fraud detection systems recognize attempts to fraud, while fraud prevention systems prevent it from occurring. While it is logical to use both in unison, prevention systems lead to hackers changing their strategies, which affects detection ability. Similarly, the existence of a detection system makes hackers devise novel ways to access confidential data, which weakens the system’s own detection abilities. According to Bart Baesens, an expert in fraud analytics, and author of a book on fraud detection, techniques to detect or reduce fraudulent activities include deive, predictive and social network analytics.Deive analytics tracks behavior that is unusual or deviates from the norm, using techniques such as association rules, clustering, and peer group analysis. Predictive analytics uses historical data sets containing real fraudulent transactions to create fraud detection models that can be subsequently used to detect fraud in real-time data. Over time, the models have to continue to learn as new types of cyber-attacks are discovered. Techniques used to analyze fraudulent data sets include neural networks, random forests, and linear / logistic regression.Companies are increasingly turning to Social Network Analysis (SNA) to combat fraud. SNA helps detect fraud patterns across functions and products lines, beating earlier limitations caused by departments working in silos. It’s advanced visual and analytics capabilities enables firms to detect and prevent fraud through online or traditional business channel.Forensic Data Analytics ToolsSince most companies nowadays deal with huge volumes of sensitive online data and are well aware of cyber fraud, you would expect to see a trend towards adoption of sophisticated anti-fraud technologies. Unfortunately, that is not the case as a study(9) by EY indicates that firms are still using traditional deive techniques for forensic data analytics and are slow to leverage more advanced technologies such as SAS, Hadoop and ACL. One reason why firms may find this challenging is due to the lack of employees with the required skills to operate more sophisticated technologies.图: EY-Global Forensic Data Analysis Survey(9)Companies Fighting Cyber Fraud on the FieldForensic accountants dig deep into numbers to identify patterns: seeking out repeating figures, and discrepancies in totals and the reasons behind them – all this comes under data analytics. One common approach used by accounting firms to detect anomalies is the application of Benford’s Law which states that 30.1% of numbers in a data set of financial transactions should begin with the number 1. Numbers starting with 2 will represent a smaller proportion of the data set and so on. This technique can be seen in action when applied to Enron’s financial statement for the year 2000 where clear variations from Benford’s Laws are observed.图: Data Analysis to Catch Cyber Fraud(10)Los Angeles County has been using SAS solutions to identify fraudulent social services claims since 2011. Predictive analytics along with social network analysis (SNA) and analytics were used to analyze social networks and calculate the likelihood of child care fraud in the Child Care Program. The Social Network Analysis component of the solution was highly valued as it allowed investigators to easily locate previously undetectable relationships based on matching telephone numbers and addresses.Memorial Health System is the second-largest public healthcare network in the US and produces massive documentation manually for vendors every year. In collaboration with IBM, the group developed VETTED, a vendor-credentialing system that gives Memorial staff greater visibility into their vendors’ activities and generates deep insights for better decision-making. The system successfully identified three vendors who were scheming to price fix a proposal. Other benefits included highlighting risky vendors and conflicts of interest.What Does the Future Hold?Despite these advances, according to a 2015 Deloitte poll(11), 1/5th of surveyed companies are not leveraging data science and analytics to counter fraud, despite expectations that fraud will increase and become tougher to detect in the next year. A PWC survey(12) revealed that a surprisingly high proportion of companies are ill-equipped to combat cybercrime attacks. Only 37% of firms surveyed had an effective response mechanism, most of them belonging to the heavily regulated financial sector. Nearly 30% had no definitive plan to counter an attack, out of which half believe they are secure enough to not require one. The survey suggests that the lack of attention is due to low interest by board members who lack the technological insight required to perceive cyber crimes as an imminent threat.Companies must start valuing the contributions of data analytics in detecting and countering fraud in a time when technology has made it easier to carry out complicated fraud schemes anonymously. What will it take for complacent organizations to take cyber fraud more seriously? Perhaps a face to face meeting with a ransomware note on a Monday morning telling the business that in order to be able to decrypt and use its own data, bitcoins must be purchased and deposited to an untraceable address.图: Nanolocker Ransomware Ananlysis (13)End NotesResearch shows that not only are all industries affected by cyber-crimes but the damage done by technology fraud will grow to become a $2.1 trillion problem by 2019. With the never-ending headlines of cyber-crimes, you would expect organizations to take measures to protect their assets. That is not the case. Instead of using sophisticated technology tools and techniques to fight fraud, many organizations are still relying on primitive tools for forensic data analytics. A PWC survey found that only 37% of firms surveyed had an effective response mechanism. Unless companies replace complacency with a sense of urgency, we will continue to see a rise in cyber-fraud.References:
https://www.statista.com/statistics/193436/average-annual-costs-caused-by-cyber-crime-in-the-us/
https://assets.kpmg.com/content/dam/kpmg/pdf/2016/05/profiles-of-the-fraudster.pdf
https://nhlearningsolutions.com/Portals/0/Documents/2015-Cost-of-Data-Breach-Study.PDF
https://www.itworldcanada.com/article/28-per-cent-of-canadian-firms-hit-by-cybercrime-in-the-last-24-months-survey/381106
https://www.juniperresearch.com/press/press-releases/online-transaction-fraud-to-more-than-double-to-$2
https://www.marketingtechnews.net/news/2016/jun/14/spending-online-fraud-prevention-soar-30-2020/
https://www.healthcareitnews.com/news/hackers-swipe-anthem-data-huge-breach-attack
https://www.emc.com/collateral/white-papers/h12105-cybercrime-healthcare-industry-rsa-wp.pdf
https://www.ey.com/Publication/vwLUAssets/EY-Global-Forensic-Data-Analytics-Survey-2014/$FILE/EY-Global-Forensic-Data-Analytics-Survey-2014.pdf
https://www.wsj.com/articles/accountants-increasingly-use-data-analysis-to-catch-fraud-1417804886
https://www2.deloitte.com/us/en/pages/about-deloitte/articles/press-releases/deloitte-poll-on-fraud-analytics-rare-event-modeling.html
https://www.pwc.com/gx/en/services/advisory/consulting/forensics/economic-crime-survey/cybercrime.html
https://blog.malwareclipboard.com/2016/01/nanolocker-ransomware-analysis.html
翻译:灯塔大数据


网友评论
最新评论
扮演了非常重要的角色,因为它能让调查员轻松定位之前没被发现的电话号码和地址的匹配关系。 “纪念卫生系统”是美国第二大的公共医疗网络,每年都会为商家提供大量的人工数据文件。通过与IBM合作,他们研发出了VETTED,一套商家资格认证系统,这能帮助
ing traditional deive techniques for forensic data analytics and are slow to leverage more advanced technologies such as SAS, Hadoop and AC
erest by board members who lack the technological insight required to perceive cyb